2025 Edition
15 min read
Enterprise Focus
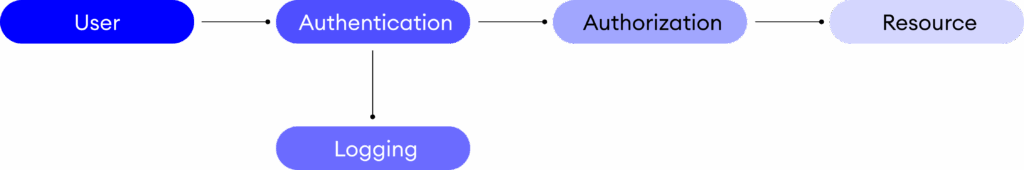
IAM enables organizations to authenticate and authorize users, monitor access, and enforce policies, ensuring that only the right people access the right resources at the right time. By anchoring security to identity, IAM mitigates threats such as credential theft, insider breaches, and unauthorized data access.
Framing IAM as both a technical control and a governance imperative elevates its visibility in risk-management forums. Embedding identity controls within enterprise risk management (ERM) ensures that access decisions align with board-approved risk appetites, regulatory mandates, and business continuity objectives.
Attackers trick users into revealing passwords
Malicious or negligent employees exploiting privileged access.
Users gain access to resources beyond their intended role
Active user sessions are compromised
Compliance Pressures
Identity and Access Management is a framework of technologies and policies that ensures only authorized individuals access specific resources. It answers three fundamental questions:
(Authentication)
(Authorization)
(Auditing)
IAM encompasses the following core capabilities
Automating the creation, management, and removal of user accounts across systems to ensure that only the right individuals retain access at the right times.
Assigning permissions based on user roles, responsibilities, or contextual attributes, ensuring access aligns with business needs and security policies.
Strengthening authentication by requiring multiple forms of verification, reducing the risk of credential theft and unauthorized access.
Providing detailed audit trails and real-time visibility into access activity to support compliance, forensics, and continuous monitoring.
Streamlining user experience by allowing individuals to log in once and securely access multiple applications without repeated credential prompts.
Securing and monitoring accounts with elevated permissions, protecting critical systems and sensitive data from misuse or compromise.
Enabling consistent enforcement of access policies, segregation of duties, and compliance with regulatory requirements.
Authentication is the first line of defense. It verifies that the user is who they claim to be.
Security Impact
After authentication, authorization governs what a user can do.
Security Impact
Reduces the attack surface by ensuring users can’t access unnecessary systems or data.
Security Impact
The Zero Trust model “never trust, always verify” relies heavily on robust IAM.
Outcome | Description |
|---|---|
Improved Security | Prevents unauthorized access, reduces credential theft |
Compliance Readiness | Automates enforcement of GDPR, HIPAA, NDPA, ISO, and more |
Operational Efficiency | Automates provisioning, reduces IT overhead |
Better Incident Response | Quick access revocation and audit trails support investigation |
Enhanced User Experience | SSO and self-service options improve productivity |
Measurable ROI | Up to 60% reduction in credential-related cyber incidents, and about 35% lower access-request processing costs |
IAM Is an Investment with Tangible Returns
Telecommunications
Start with Identity Inventory: Understand all identities (employees, contractors, partners, systems).
Use Strong Authentication: Implement MFA and biometrics where possible.
Apply Least Privilege Access: Limit permissions to reduce exposure.
Integrate with HR and IT Systems: Automate provisioning and deprovisioning.
Define and Track IAM KPIs: Including time-to-provision/deprovision, number of privileged-access exceptions, and mean time to detect/respond to identity incidents.
Monitor Continuously: Use real-time analytics to detect unusual activity.
Educate Users: Raise awareness on access policies and phishing risks.
Challenge | Mitigation Strategy |
|---|---|
Legacy Systems Integration | Use APIs, connectors, or middleware |
User Resistance | Communicate benefits and provide training |
Complex Access Policies | Start small, use templates, refine over time |
Performance Overheads | Use scalable IAM platforms with cloud-native architecture |
The future of IAM is adaptive, decentralized, and AI-powered. Key trends include:
IAM will be increasingly embedded into applications and APIs as organizations adopt zero-trust architectures.
As organizations navigate a complex cybersecurity landscape, IAM has become a foundational pillar of digital defense. It shifts the focus from infrastructure to identity, providing the control, visibility, and intelligence needed to secure access at scale.
Fixiam, as a next-generation IAM solution, embodies this shift. By combining biometric MFA, policy-driven access control, and continuous monitoring, Fixiam enables organizations to confidently manage identities across cloud, on-prem, and hybrid environments.
Whether you’re safeguarding financial systems, securing telecom infrastructure, or managing public-sector platforms, IAM is no longer optional. It is the enabler of trust, security, and resilience in the digital age.
Fixiam is a robust Identity and Access Management platform designed for modern enterprises. From biometric authentication to real-time access insights, Fixiam helps organizations secure digital identities, enforce zero-trust policies, and meet global compliance standards.
Explore more at https://seamfix.com/fixiam